User guidance and responsibilities
-
- Part of:
- Trust Centre
Explains the security rules you should follow when using Hwb.
Overview
The guidance provided is generic in nature but reflects a typical school’s usage based on information from stakeholders including teachers, support staff and local authorities.
General advice
All users should follow basic general security rules; these are generally applicable to any IT system and include:
- never let anyone else use your Hwb account
- never use someone else’s Hwb account
- do not create generic or shared accounts
- follow good password guidelines (see Hwb security guidance)
- be mindful when using your Hwb account in a public place, ensure that your usage cannot be observed, especially when entering your password
- don’t use your Hwb account for purposes other than related to education business
- always check e-mail recipient details are correct before sending
- always report concerns about inappropriate usage, local procedures should be followed as necessary
- avoid use of public, shared or personal devices / systems for sensitive or personal data
The use of personal devices, often referred to as ‘Bring Your Own Device’ (BYOD), will almost certainly introduce risks to the information processed on them, this is each organisation’s risk management decision.
The ICO has published specific guidance with respect to BYOD and data protection.
Hwb is not currently configured to control or check the devices accessing Hwb, instead there is a reliance on users following the local policies that are applicable to them.
Information security
The intention of information security is to preserve the following properties:
- confidentiality: ensuring information remains secret
- integrity: ensuring the accuracy of information
- availability: ensuring information can be accessed when required
In addition to these key attributes, there will be scenarios in which other properties will be of importance for example, accountability, non-repudiation and reliability.
Personal data
Information about identifiable individuals is personal data, the General Data Protection Regulations (GDPR) define the legal requirements applicable to the use of personal data.
The UK’s Data Protection Act was revised in 2018 and enacts the GDPR requirements in UK law.
The revised definition of personal data is included in the Privacy notice.
The precautions that should be taken are applicable irrespective of media type. For example, each of the following can require security measures if they contain personal data:
- e-mails
- photos
- electronic documents
- hand written notes
This guidance is limited to controls applicable to electronic formats of data, if information is printed out it still needs to be protected, procedures should be consistent with those applicable to electronic documents.
The Information Commissioner’s Office (ICO) publishes guidance and codes of practice applicable to data protection and personal data on their website.
Hwb specifics
Hwb has been designed primarily to store educational content that can be shared with any other Hwb user.
Hwb has standard controls as default, so it is suitable for the basic personal data required for day to day use of the system.
Enhanced controls are available. For more information please visit security controls.
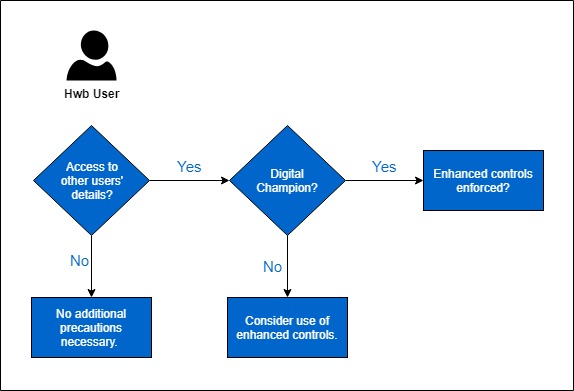
User Management Portal (UMP)
The UMP is a bespoke solution that provides Hwb users with access to account management facilities.
For the majority of users standard controls in the UMP will be appropriate but for some levels of access, enhanced controls are recommended or required.
Google Workspace for Education Fundamentals and Microsoft 365
Hwb provides users with access to both Google Workspace for Education Fundamentals and Microsoft 365. Both services have a range of controls suitable for processing personal data and OFFICIAL information, which makes them the most appropriate Hwb services for working on and storing such data.
A summary of the relevant underlying governance information applicable to Google Workspace for Education Fundamentals and Microsoft 365, as managed by Google and Microsoft respectively, is included in Data Compliance.
For the majority of Hwb users the default configuration of Google Workspace for Education Fundamentals and Microsoft 365 will provide them with security appropriate information they have access to.
Where Hwb users access or exchange sensitive information there may be a need for a greater level of protection. Therefore, optional additional controls are available.
-
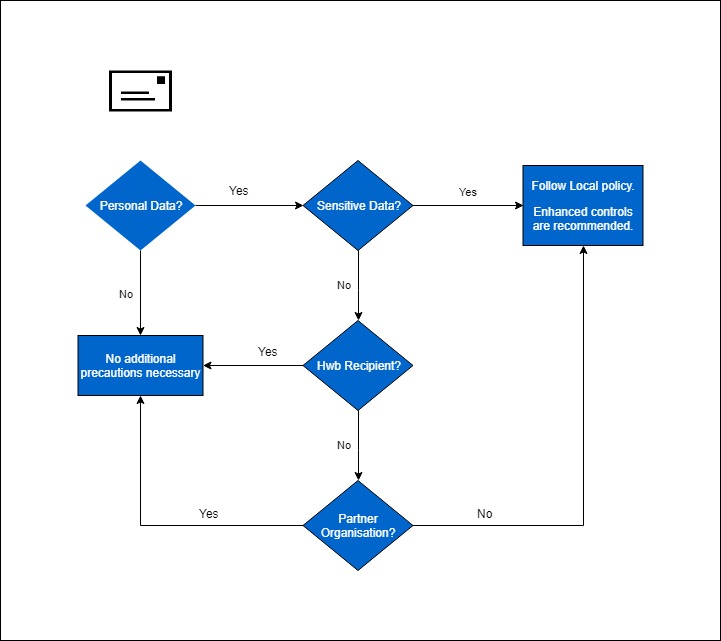
Microsoft 365 is the e-mail system provided for all users of Hwb (learners require consent). It is a standards-based e-mail system that benefits from a number of configuration options that can provide robust security.
The default configuration of Microsoft 365 provides a secure way of sending e-mail between Hwb users as well as some partner organisations. Our current list of verified partner organisations.
The list of partner organisations that are configured to receive secure e-mail from Hwb is established in conjunction with local authorities and regional education consortia.
Note: Until a partner organisation has been verified it should be assumed that e-mails will not be secure and enhanced controls considered.
Microsoft 365 has additional options for encrypting sensitive e-mail. Further guidance should be sought from your headteacher or local authority information security officer as required. For more information please visit Security controls.
The following flowchart provides a graphical representation of the recommended decision process for deciding the appropriate encryption method for e-mails containing personal data and a similar process can be applied to other sensitive data.
-
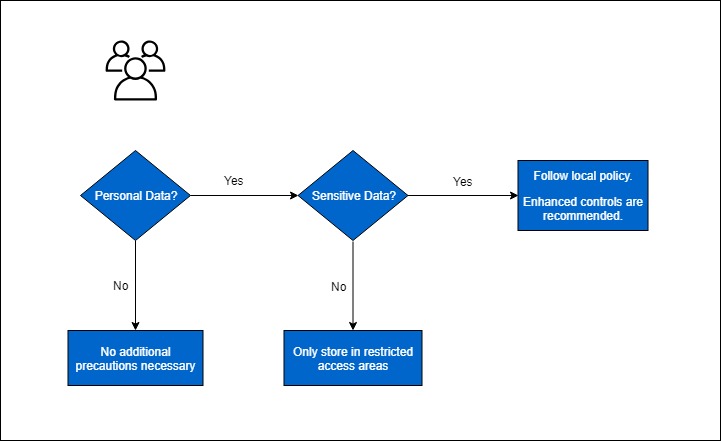
Google for Education and Microsoft 365 both have options for working collaboratively:
Google for Education:
- Classroom
- Team Drives
- Sites
Microsoft 365:
- Teams
- Groups
- SharePoint
(incorporates both directory and site functionality)
With a potentially large number of users with access to shared working areas, care should be taken when storing sensitive data in these areas.
Specific areas for securely collaborating with sensitive data can be configured to help ensure:
- access is constrained to those with a need to know the information
- enhanced protection for documents to reduce the risk of accidental release of information
For more information please visit Security controls.
Note: The enhanced level of protection for documents can necessitate the use of the desktop version of Microsoft 365 for creating and editing documents.
For staff with regular access to the most sensitive data additional security controls are available and should be considered (to help prevent password-based attacks).
-
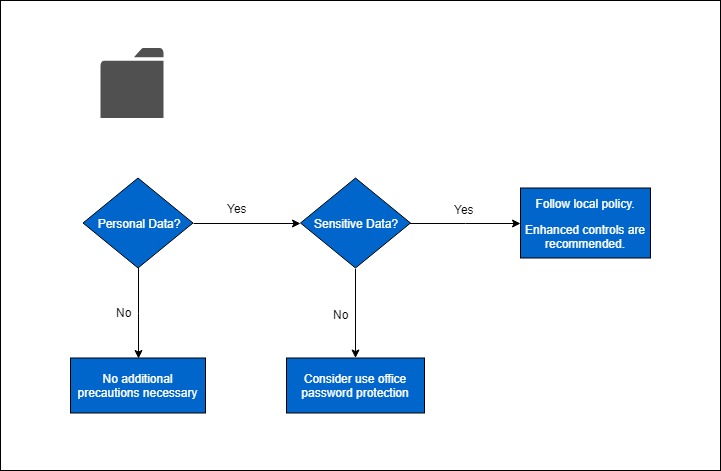
Hwb provides each user with access to Google Drive and Microsoft OneDrive.
Note: Password protection is available in desktop versions of Microsoft 365.
Password protection of individual files containing sensitive data can be an effective way of ensuring only those with the password can access the contents if confidentiality is a concern.
In such situations advice should be sought about password complexity, length and distribution. Password guidance is available below.
Hwb Security Guidance
Passwords
For IT systems, and in particular cloud services such as Microsoft 365 and Google Suite for Education, passwords are a necessary inconvenience and probably will be for the foreseeable future. They are currently the most appropriate option for ensuring that only you have access to your account.
To try and make it simpler for Hwb users to manage their passwords, the Hwb Platform has been designed so that you only need one password across the platform, this is called Single Sign-On or SSO.
An associated implication of having one password for access to multiple systems is that if someone gains access to your password they can potentially access a wide range of information. For this reason it is important to understand what you can do to ensure your password is not susceptible.
This guidance is intended to help ensure your Hwb account remains secure, but it is equally applicable to passwords you use for personal accounts, for example online banking.
-
There are many desirable properties for passwords, but this guidance will focus primarily on the properties that are effective for preventing hackers. An effective password would be:
- unique
- difficult to guess
Other desirable properties of passwords sometimes conflict with these. For example ideally a password is easy to remember, but this often results in passwords that are easy to guess or are not unique (an alternative option to easily remembered passwords is recommended below).
-
There are two main ways hackers can try to gain access to passwords:
Hacking password systems
If a website is hacked, the hackers might be able to gain access to the password system and copy all the passwords used on the site. They can use these passwords to takeover individual accounts.
Phishing attacks
Phishing attacks will usually only compromise one password at a time, but they do not require hacking into a system first.
If hackers are able to match a password to your identity, for example via your registered e-mail address or a username, they will try to use the password to access other systems.
For example, if your social media password is the same as your online banking password and a hacker accesses the passwords used on social media they may be able to access your online banking as well.
While having unique passwords will not help prevent an initial attack being successful, it will prevent subsequent attacks against other systems that you use.
-
Some hacking attacks are based on someone trying to access an account by trying to guess passwords, usually this type of attack is based on hackers having a list of passwords that they can use in automated attacks. The lists can be based on combinations of the following information:
- keyboard patterns, for example ‘1q2w3e4r’
- common passwords observed from hacked systems, for example ‘sunshine’
- names of sports, films, singers or other popular themes
Most systems, including Hwb, have controls to slow down online password guessing attacks, but it is not possible to completely eliminate them.
-
One of the desirable properties for passwords is that they are easy to remember, but for most people this is not practical without either:
- selecting common words as passwords
- recycling passwords across systems
- using a repeatable and predictable format
None of the above options results in a password that will reliably resist hacking attacks.
One alternative to trying to remember multiple passwords is to use a password manager, this is an application that will store all your passwords so that you do not need to remember them. Using a password manager means you can use:
- impossible to guess passwords that are highly resistant to brute-force attacks
- a different password for every site you register on
Many password managers can be synchronised across devices or backed up online to avoid single points of failure.
Using a password manager is highly recommended.


